This file is an 32bits elf binary, compiled from go language (i guess ... coded by @nibble_ds ;)
The binary has some debugging symbols, which is very helpful to locate the functions and api calls.
GO source functions:
- main.main
- main.function.001
If the binary is executed with no params, it prints "Nope!", the bad guy message.
~/ncn$ ./inbincible
Nope!
Decompiling the main.main function I saw two things:
1. The Argument validation: Only one 16 bytes long argument is needed, otherwise the execution is finished.
2. The key IF, the decision to dexor and print byte by byte the "Nope!" string OR dexor and print "Yeah!"
 |
| The incoming channel will determine the final message. |
 |
| Dexor and print each byte of the "Nope!" message. |
This IF, checks 16 times if the go channel reception value is 0x01, in this case the app show the "Yeah!" message.
Go channels are a kind of thread-safe queue, a channel_send is like a push, and channel_receive is like a pop.
If we fake this IF the 16 times, we got the "Yeah!" message:
(gdb) b *0x8049118
(gdb) commands
>set {char *}0xf7edeef3 = 0x01
>c
>end
(gdb) r 1234567890123456
tarting program: /home/sha0/ncn/inbincible 1234567890123456
...
Yeah!
Ok, but the problem is not in main.main, is main.function.001 who must sent the 0x01 via channel.
This function xors byte by byte the input "1234567890123456" with a byte array xor key, and is compared with another byte array.
=> 0x8049456: xor %ebp,%ecx
 |
| This xor, encode the argument with a key byte by byte |
The xor key can be dumped from memory but I prefer to use this macro:
(gdb) b *0x8049456
(gdb) commands
>i r ecx
>c
>end
(gdb) c
Breakpoint 2, 0x08049456 in main.func ()
ecx 0x12 18
Breakpoint 2, 0x08049456 in main.func ()
ecx 0x45 69
Breakpoint 2, 0x08049456 in main.func ()
ecx 0x33 51
Breakpoint 2, 0x08049456 in main.func ()
ecx 0x87 135
Breakpoint 2, 0x08049456 in main.func ()
ecx 0x65 101
Breakpoint 2, 0x08049456 in main.func ()
ecx 0x12 18
Breakpoint 2, 0x08049456 in main.func ()
ecx 0x45 69
Breakpoint 2, 0x08049456 in main.func ()
ecx 0x33 51
Breakpoint 2, 0x08049456 in main.func ()
ecx 0x87 135
Breakpoint 2, 0x08049456 in main.func ()
ecx 0x65 101
Breakpoint 2, 0x08049456 in main.func ()
ecx 0x12 18
Breakpoint 2, 0x08049456 in main.func ()
ecx 0x45 69
Breakpoint 2, 0x08049456 in main.func ()
ecx 0x33 51
Breakpoint 2, 0x08049456 in main.func ()
ecx 0x87 135
Breakpoint 2, 0x08049456 in main.func ()
ecx 0x65 101
Breakpoint 2, 0x08049456 in main.func ()
ecx 0x12 18
The result of the xor will compared with another array byte, each byte matched, a 0x01 will be sent.
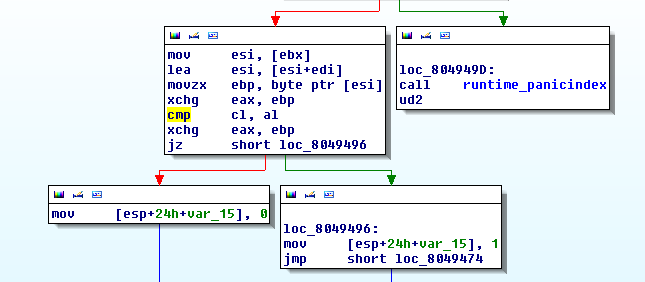 |
| The cmp of the xored argument byte, will determine if the channel send 0 or 1 |
(gdb) b *0x0804946a
(gdb) commands
>i r al
>c
>end
At this point we have the byte array used to xor the argument, and the byte array to be compared with, if we provide an input that xored with the first byte array gets the second byte array, the code will send 0x01 by the channel the 16 times.
Now web have:
xorKey=[0x12,0x45,0x33,0x87,0x65,0x12,0x45,0x33,0x87,0x65,0x12,0x45,0x33,0x87,0x65,0x12]
mustGive=[0x55,0x75,0x44,0xb6,0x0b,0x33,0x06,0x03,0xe9,0x02,0x60,0x71,0x47,0xb2,0x44,0x33]
Xor is reversible, then we can get the input needed to dexor to the expected values in order to send 0x1 bytes through the go channel.
>>> x=''
>>> for i in range(len(xorKey)):
... x+= chr(xorKey[i] ^ mustGive[i])
...
>>> print x
G0w1n!C0ngr4t5!!
And that's the key :) let's try it:
~/ncn$ ./inbincible 'G0w1n!C0ngr4t5!!'
Yeah!
Got it!! thanx @nibble_ds for this funny crackme, programmed in the great go language. I'm also a golang lover.
Read more
- Nsa Hacker Tools
- Best Pentesting Tools 2018
- Hack Tools Download
- Hacker Tools List
- Install Pentest Tools Ubuntu
- Pentest Tools Open Source
- Hacking Tools Pc
- Hacking App
- Hacker Tools List
- Hacker Tools Software
- Pentest Tools Nmap
- Hack Tools
- Hacking App
- Pentest Recon Tools
- Hack Tools Online
- Termux Hacking Tools 2019
- Hack Tools For Games
- Hack Tools For Mac
- Hacking Tools Kit
- Hacker Security Tools
- Free Pentest Tools For Windows
- Nsa Hack Tools
- Pentest Tools For Mac
- Pentest Tools Kali Linux
- Hacker Tools Online
- Hacker Tools List
- New Hacker Tools
- Pentest Tools Github
- Hacking Tools Name
- Pentest Reporting Tools
- Hacking Tools For Games
- Hacker Hardware Tools
- What Is Hacking Tools
- Hacker Tools 2020
- Pentest Tools Download
- Nsa Hacker Tools
- Hacker Search Tools
- Pentest Tools Review
- Hacker Tools List
- Hacker Tools Mac
- Pentest Tools Framework
- Pentest Recon Tools
- Pentest Tools Website Vulnerability
- Bluetooth Hacking Tools Kali
- Hacker Security Tools
- Hacking Tools Software
- Hacking Tools For Windows 7
- Pentest Tools Tcp Port Scanner
- Hack App
- Hack Rom Tools
- Pentest Reporting Tools
- Hacking Tools Github
- Hack Tools Download
- Pentest Tools Url Fuzzer
- Pentest Tools Github
- Hacking Tools Pc
- Nsa Hacker Tools
- Hackers Toolbox
- Hackers Toolbox
- Pentest Tools Port Scanner
- Pentest Tools Tcp Port Scanner
- Free Pentest Tools For Windows
- Hacking Tools For Windows
- Physical Pentest Tools
- Github Hacking Tools
- Pentest Tools Free
- Hack Tools Download
- Hack Tools Download
- Hack Website Online Tool
- Hack Tools
- Hacker Security Tools
- Best Pentesting Tools 2018
- Hacking Tools Hardware
- Ethical Hacker Tools
- Hack Tool Apk
- Pentest Tools Framework
- Pentest Tools Bluekeep
- Pentest Tools Tcp Port Scanner
- Nsa Hack Tools Download
- Beginner Hacker Tools
- Pentest Recon Tools
- Free Pentest Tools For Windows
- Nsa Hack Tools
- Free Pentest Tools For Windows
- Hacking Tools For Mac
- Hacking App
- Hacker Tools For Pc
- Kik Hack Tools
- Pentest Tools Free
- Tools For Hacker
- Pentest Tools Open Source
- Pentest Tools
- Pentest Tools Kali Linux
- Hack And Tools
- Hack Tools For Mac
- Nsa Hack Tools Download
- Hacker Tools For Pc
- Hacking Tools Free Download
- Blackhat Hacker Tools
- Hacking Tools For Beginners
- Hacking Tools Kit
- Bluetooth Hacking Tools Kali
- Hacking Tools
- Hacking Apps
- Hacking Tools 2020
- Pentest Tools Website
- Hacker Tools 2019
- Beginner Hacker Tools
- How To Install Pentest Tools In Ubuntu
- Pentest Tools Alternative
- Hacker
- Kik Hack Tools
- Hacker Techniques Tools And Incident Handling
- Hack Tools 2019
- Hacking Tools For Pc
- Pentest Tools Windows
- Hack Tools 2019
- Hack Website Online Tool
- Black Hat Hacker Tools
- Kik Hack Tools
- Hacker Tools For Pc
- Pentest Automation Tools
- Best Hacking Tools 2019
- Hack Tools Pc
- Pentest Tools Apk
- Pentest Tools Alternative
- Hack Tools Online
- Hack Tools For Windows
- Hacker Tools Software
- Hack Tools 2019
- Computer Hacker
- Pentest Tools Framework
- Pentest Recon Tools
- Hacking Tools For Windows Free Download
- Hacker Tools Linux

No comments:
Post a Comment